LDAP Authentication
NOTE
The LDAP Authentication screen is not available for the HP LaserJet M3027mfp and
M5025mfp products.
Use the LDAP Authentication page to configure a Lightweight Directory Access Protocol (LDAP) server
to authenticate device users. When LDAP authentication is selected as the Log In Method for one or
more Device Functions on the Authentication Manager page, the user at the device must enter valid
credentials (username and password) to gain access to those functions.
Authentication consists of two interdependent parts. First, the device verifies the user's credentials with
the LDAP server. After the device user has supplied valid credentials and has been authenticated, the
device searches for the user's e-mail address and name. If either step fails, the user is denied access
to the functions that have been configured to require LDAP authentication.
Use the LDAP Authentication page to set up the parameters that are used to access the LDAP server
and searches for the user's information. Note that this page only applies when LDAP is selected as a
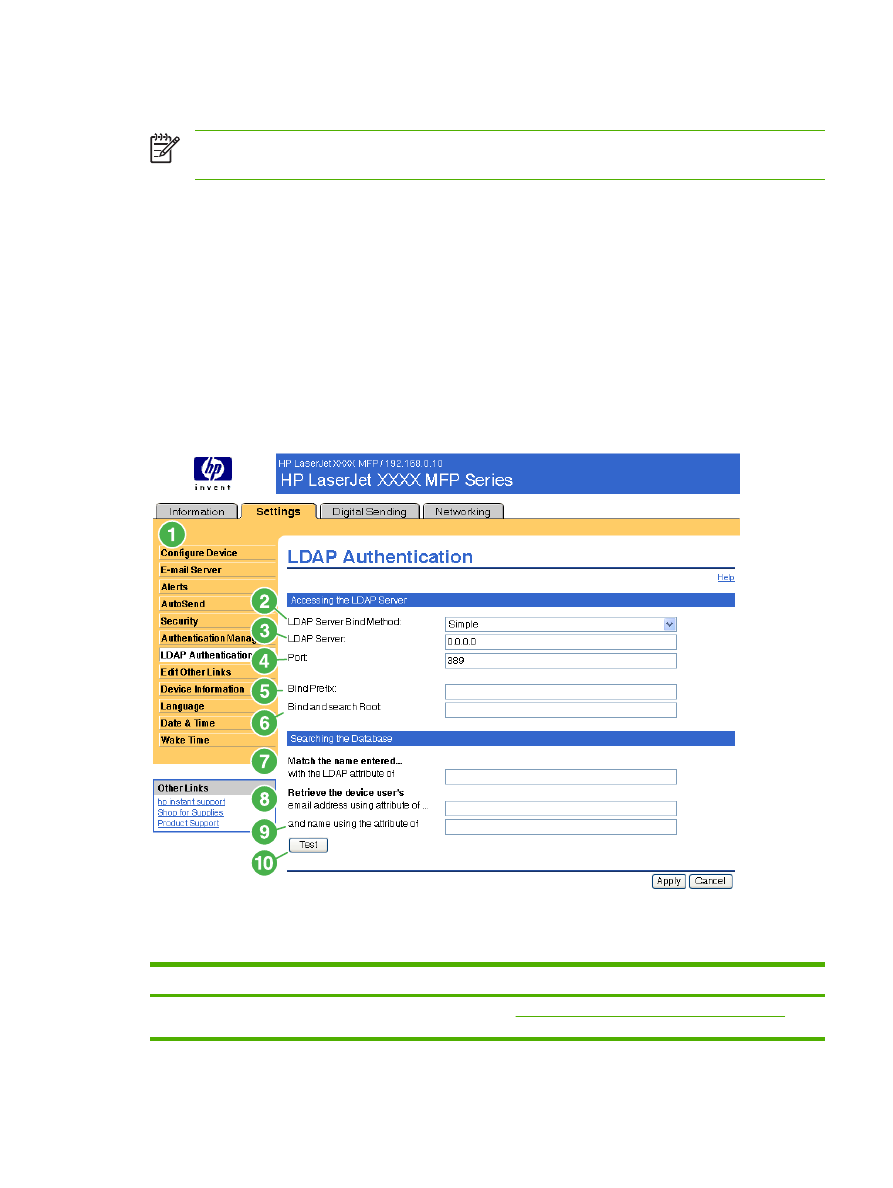
Log In Method on the Authentication Manager page. The following illustration and table describe how
to use this screen.
Figure 3-9
LDAP Authentication screen
Table 3-8
LDAP Authentication
Callout
Area on the screen
Information or capability that the area provides
1
HP EWS tabs and
menus
For more information, see
Navigating through the HP Embedded Web Server
.
ENWW
LDAP Authentication
41
Callout
Area on the screen
Information or capability that the area provides
2
LDAP Server Bind
Method
The LDAP Server Bind Method setting determines how the device will access the
LDAP server. Contact your LDAP server administrator to determine which method
will work best for you.
●
Simple - The selected LDAP server does not support encryption. Note that the
password, if any, will be sent unencrypted across the network.
●
Simple over SSL - The selected LDAP server supports encryption using the
Secure Sockets Layer (SSL) protocol. All data, including the username and
password, will be encrypted. The LDAP server must be set up to support SSL,
including configuring a certificate that establishes its identity.
Also, the device network interface must be configured with a Certificate Authority
(CA) certificate to validate the LDAP server. The CA certificate is configured on
the Networking tab of the Web interface. In some LDAP server configurations,
a client certificate is also required and is configured on the same Networking
tab.
3
LDAP Server
The LDAP Server setting is the host name or IP address of the LDAP server to be
used to authenticate device users. When using SSL, the name or address typed here
must match the name in the certificate that the server sends.
Multiple servers can be included in this field by separating their addresses with a
vertical bar ('|', ASCII 0x7c) character. This feature can be used, for example, to
specify primary and backup servers. The network interface only supports a single
Certificate Authority (CA) certificate, so all the LDAP servers in the list must use the
same CA.
4
Port
The Port setting refers to the TCP/IP port number on which the server is processing
LDAP requests. Typically, this is port 389 for Simple binds or 636 for Simple over SSL
binds.
5
Bind Prefix
The Bind Prefix setting is the LDAP attribute used to construct the user's
Distinguished Name (DN) for authentication. This prefix is combined with the
username typed at the control panel to form the Relative Distinguished Name (RDN).
Commonly used prefixes are "CN" (for common name) or "UID" (for user identity).
6
Bind and search Root
When the Use Device User’s Credentials method is selected, the Bind and Search
Root value is used during both phases of authentication. During the credential
verification phase, this value is combined with the RDN to construct the full
Distinguished Name (DN) of the user. During the user information searching phase,
this value is the DN of the LDAP entry where the search begins.
When the Use Administrator Credentials method is selected, the Bind and Search
Root is only used as a search root. The Search Root of the base of the LDAP directory
can be specified, and the device will search the entire LDAP tree for the user object
corresponding to the username entered at the device.
7
Match the name entered
with the LDAP attribute
of
When searching for the device user's information in the LDAP database, the contents
of the attribute specified in this field are compared to the username that was typed
during authentication. This attribute is usually the same as the Bind Prefix.
8
Retrieve the device
user's e-mail address
using attribute of
After the device user has been located in the LDAP database, the user's e-mail
address is retrieved from the database by using the LDAP attribute specified in the
e-mail address using attribute of field.
9
and name using the
attribute of
The user's display name is obtained from the LDAP attribute that is specified in the
name using attribute of field.
10
Test
Use the Test feature to test the validity of your settings before applying them. When
you click this button, you are asked to provide user credentials as if you were logging
in at the device control panel. If the credentials that you provide are authenticated
and the user information is found in the LDAP database, a success message appears.
Otherwise, an error message appears indicating why authentication failed.
Table 3-8
LDAP Authentication (continued)
42
Chapter 3 Configuring the product from the Settings screens
ENWW